Biometric Access Control For Your Business
While an access card or password can be misplaced, stolen, or cloned, Biometric access solutions ensures that the only people accessing your facility are the ones who have permission. Today’s Biometric access control solutions help businesses increase security by better controlling access credentials and protecting user privacy.
What is biometric authentication?
Biometric authentication is a security process that uses your unique biological characteristics to verify that you are who you say you are. This involves a complex mathematical formula to verify you based on your physical metrics.
Simply, biometric authentication allows you to better protect secured areas. The most common types of biometric authentication are fingerprints, iris scanners, and facial recognition.
Is Biometric Access Control Right for My Business?
Facial biometrics for authentication offer the highest grade of security and the best user experience while protecting the privacy of users.
Biometrics are inherently more secure and convenient than keys, cards, and PIN codes. They are becoming increasingly popular as a security solution of the digital age, especially in the workplace. Facial recognition is perfectly suited for physical access control: unlocking doors, safes, and turnstiles for authorized personnel because it is quick and secure.
What doors are best suited for Biometric Access?
Biometric access solutions can be used for just about any door. Our solution seamlessly integrates with many leading enterprise access control systems. However, it is not always practical to replace all access points with a biometric reader. Here are 3 types of doors that may be the best fit:
These doors may require 2 factor authentication for added security. Using biometric data as one factor makes spoofing these entrances more difficult. They are also more secure because critical credentials such as pins and key cards can be shared whereas biometric data can not.
For Example: Cash rooms, evidence rooms, security rooms, data storage.
What if I don’t want to have my image included in a database?
Up until now, facial biometric authentication would compare your individual data against a database of collected images or video stills. While this is still how most facial biometric verification works, updates in facial recognition technology allow for the elimination of a picture database providing a more private experience for the user.
Stonelock, for instance, uses near-infrared technology to capture reflectivity data that is not visible to the naked eye. Mapping data points on your face but not storing any images or data such as gender, ethnicity, or age. This allows them to protect users’ privacy better than any facial biometric product on the market has before.
Speak to an Access Control Specialist Today
StoneLock delivers a frictionless, trusted, and revolutionary approach to secure facial authentication. Speak to a member of our sales team and discover how easy it is to integrate StoneLock GO.




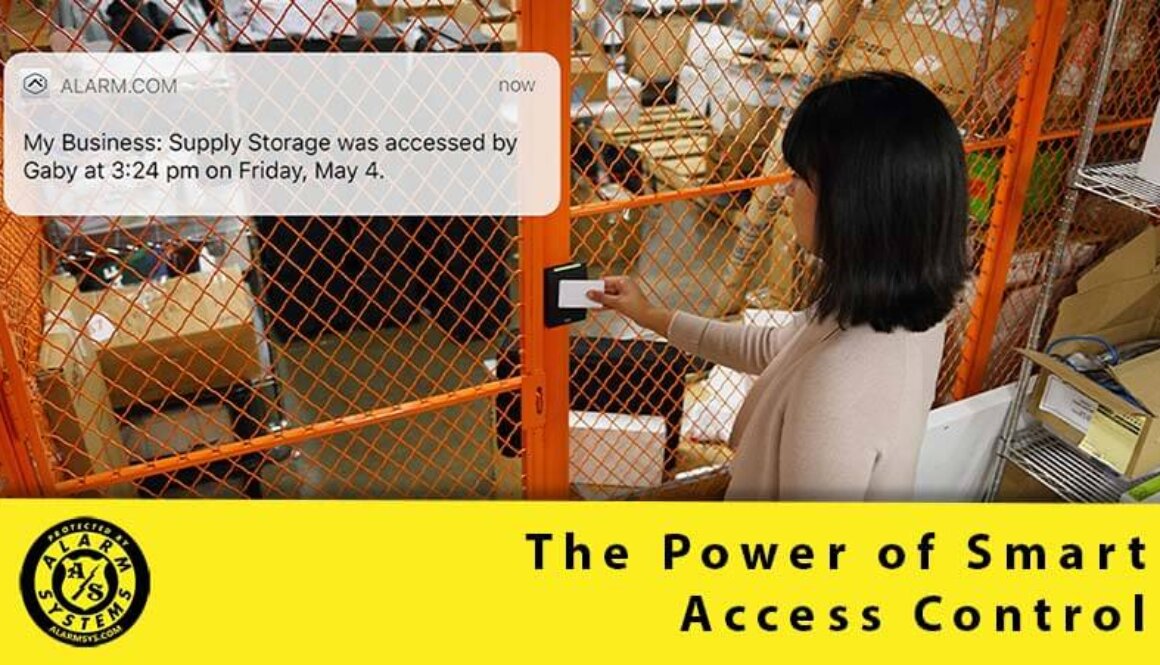

 Smart Access Control gives you the power to monitor access to your business in real time. You can easily see who has access and when they accessed. Your system can also send alerts, so you know if the office was opened on time and by who.
Smart Access Control gives you the power to monitor access to your business in real time. You can easily see who has access and when they accessed. Your system can also send alerts, so you know if the office was opened on time and by who.


 Local devices can be locked, to restrict employees from cranking up the AC or blasting heat outside your preferred range. Meanwhile, you will still have full control. Check current temperatures and make adjustments from your app quickly and easily.
Local devices can be locked, to restrict employees from cranking up the AC or blasting heat outside your preferred range. Meanwhile, you will still have full control. Check current temperatures and make adjustments from your app quickly and easily.
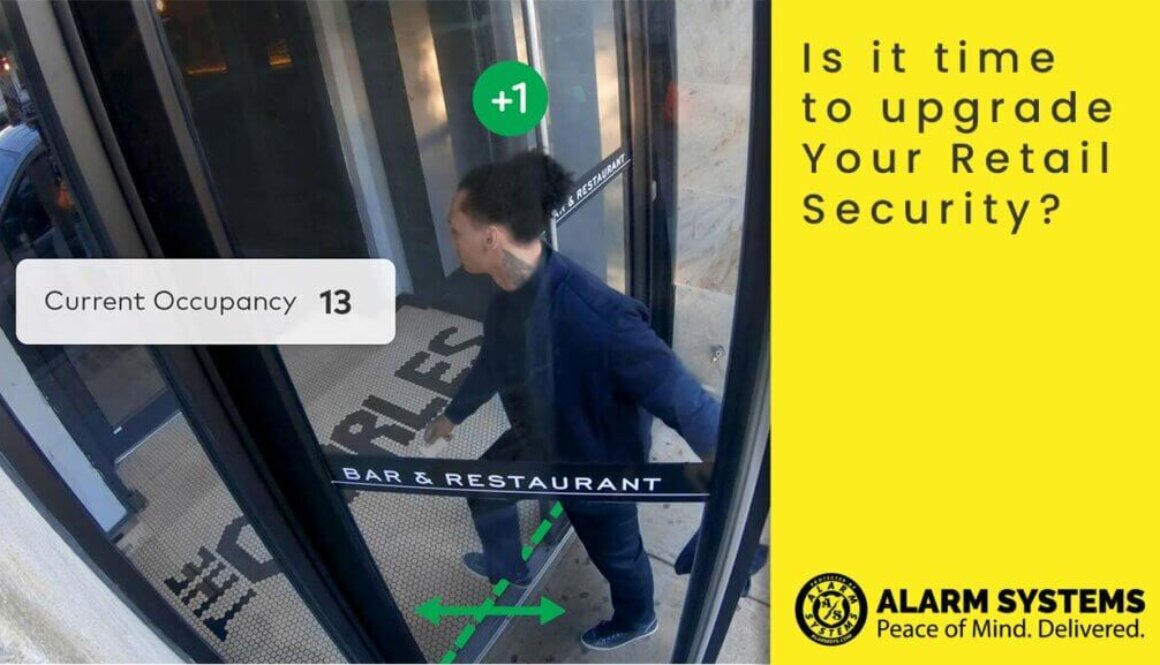
 Smart Security Systems are connected to secure networks that give business owners the freedom to step away from their businesses while remaining in control and being able to check-in. Networked security cameras allow you to access your surveillance system remotely. Enhanced with AI, your cameras become an active tool for monitoring your business, sending notifications for significant events.
Smart Security Systems are connected to secure networks that give business owners the freedom to step away from their businesses while remaining in control and being able to check-in. Networked security cameras allow you to access your surveillance system remotely. Enhanced with AI, your cameras become an active tool for monitoring your business, sending notifications for significant events.
 The Belleville Police Service reports that False Alarms are “one of the most significant misuses of police resources” and since the implementation of their False Alarm Reduction Program they have reduced the number of False Alarms they report to by 47%
The Belleville Police Service reports that False Alarms are “one of the most significant misuses of police resources” and since the implementation of their False Alarm Reduction Program they have reduced the number of False Alarms they report to by 47%

 Your Access Control system can even be used as a secondary punch clock. Because each access card or pin can be linked to a specific employee it is easy to pull reports on when they entered the building.
Your Access Control system can even be used as a secondary punch clock. Because each access card or pin can be linked to a specific employee it is easy to pull reports on when they entered the building. Customized Access
Customized Access